Integration of Workspace ONE Access as 3rd party SAML iDP in Okta
We can integrate Workspace ONE Access as 3rd party SAML iDP in Okta. That is necessary for the Device Trust Use Case for instance with iOS and Android mobile devices.
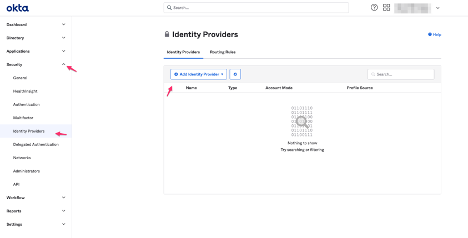
- Log into Okta
- Security
- Identity Providers
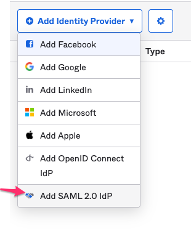
- Add Identity Providers
- Choose Add SAML 2.0 IdP
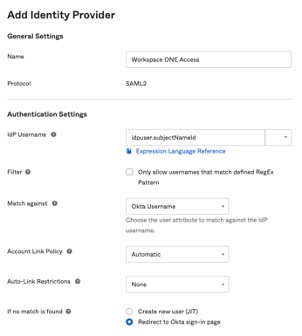
- Enter a Name (example: Workspace One Access)
- IdP Username: idpuser.subjectNameId
- If no match is found: Enable Redirect to Okta-sign-in oage
- IdP Issuer URI: Enter the entityID (that you will find in the Identity Provider metadata file from Workspace ONE Access we´ve downloaded before)
- Example: https://tenant.vmwareidentity.com/SAAS/API/1.0/GET/metadata/idp.xml

- IdP Single Sign-On: Enter the SingleSignOnService Location URL (that you will find in the Identity Provider metadata file from Workspace ONE Access we´ve downloaded before)
- Example: https://tenant.vmwareidentity.com/SAAS/auth/federation/sso

- IdP Signature Certificate: Choose the Signing Certificate file which we downloaded from Workspace ONE (Workspace ONE Access SAML Metadata)
- Check the Certificate expires in time
- Click Show Advanced Settings
- If Request Authentication Context option is not available, enable it (Settings -Features – Workspace1 Device Trust). (Depends on your Okta tenant version)
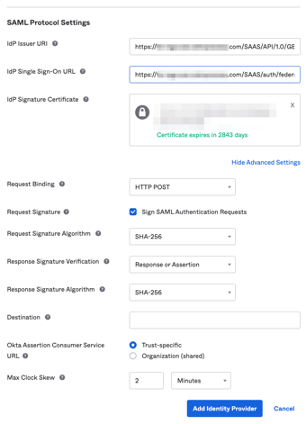
- Add Identity Provider
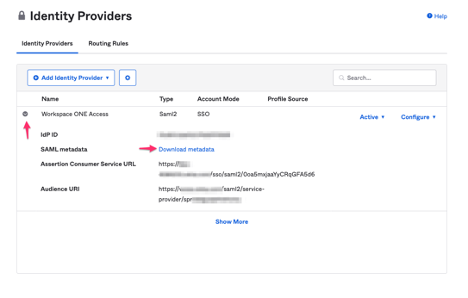
- Click the arrow near the Workspace ONE Access IdP entry
- Check that the information given we entered before
- SAML metadata, click Download metadata
- Or right click and Copy Link Address
- Save the metadata.xml file
Now the users can log into the Workspace ONE Access user portal directly from the Okta user portal via Single Sign On (SSO) if they click in the Workspace ONE button.
866 Total Views 2 Views Today
