Check Attribute mapping – Okta
To make the whole process works if you implemented the compete scenario (Workspace ONE Access and UEM, Okta and Microsoft Azure) we have to make sure that the user attribute mapping is correct. So, you have to check the attribute mapping from Okta User to Microsoft Office 365 application in the Okta tenant as well. Reason behind that is, that the immutableId attribute in Azure AD will be matches with the external ID which the user gets from Okta and is provisioned to Workspace ONE Access as ExternalID and to Workspace ONE UEM as Azure Active Directory Mapping Attribute in the user account.
Then the user can be mapped and enroll their devices into Azure AD as far as they have the license assigned and available.
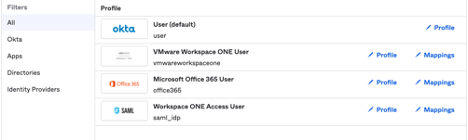
- Log into Okta
- Directory
- Profile Editor
- Click Mappings at Microsoft Office 365
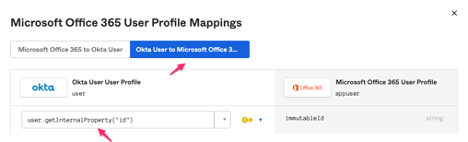
- On the top choose Okta User to Microsoft Office 365
- Enter for the immutableId user.getInternalProperty(“id”)
- Sometimes the (“) will not be correctly set. Then set it again with after all text was entered
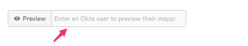
- At the bottom you can enter a user account to test the mapping in a preview
- You should see the mapping with the ExternalID from Okta
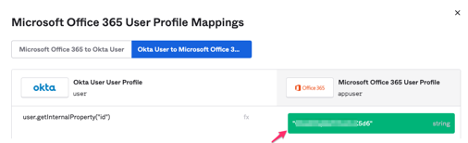
- Exit Preview
- Save Mappings
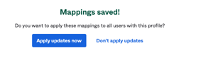
- Then you will be asked to apply these mappings to all users with this profile
- Apply updates now
- Save Mappings
1092 Total Views 2 Views Today
